Delegated Credentials for TLS a new cryptographic protocol announced by Mozilla, in collaboration with Cloudflare, Facebook and other community members of IETF.
After, ongoing development for three years by combined efforts of Facebook, Cloudflare and Firefox we can say that this new protocol is about to become an internet standard. Currently, the Internet Engineering Taskforce (IETF) is in the process of standardization to make it an internet standard.
Delegated Credential an extension to SSL/TLS Certificate. To establish an encrypted connection between the server and web browser, delegated credentials deployed on all servers with different keys.
Delegated Credential help in preventing the misuse of the misquoted certificate by reducing the validation period to a shorter period for months or hours.
Let’s understand why you need Delegated Credentials for TLS before understanding the concept of Delegated Credentials for TLS in detail.
As SSL Certificate is used to secure the connection between the web browser and server. When connected to the secured protocol, the server provides a TLS certificate to the browser to confirm the proper identity before exchanging the information.
These certificates have a validation period of 1-2 years. Sometimes before the expiration date, the certificate gets revoked for various reasons such as:
In the above situation, the only way out is to have a fresh certificate reissued.

The revocation check is done by contacting the CA’s server to get the information about the certificate’s health status.
The browser sometimes doesn’t show the message of “no longer trusted certificate” to the user after the certificate has been revoked. As a browser uses cached validation status. Also, sometimes because of the delay from the CAs CRL/OCSP servers there is a delay in response in projecting the security check results to the end-user.
Facebook and Cloudflare are collaborating in building this protocol to ensure more security for the end-users since their services are used by millions of end-users.
The time span between the certificate is revoked until it is replaced by a fresh reissued certificate, makes the website venerable to attackers.
During this time span, there are certain browsers who might project the website to be secured by using the cache data. To overcome the shortcomings, Delegated Credentials comes into the picture.
Delegated Credentials come with shorter validations and is signed by the leaf certificate issued by the CA.
IETF community has proposed Delegated Credentials for TLS to mitigate the above-mentioned issue. As it is a new cryptographic protocol that balances the trade-off between lifetime and reliability.
Delegated Credentials for TLS allows companies to take partial control over the process of signing new certificates for themselves. This certificate uses a private key with a shorter time period than the actual certificate.
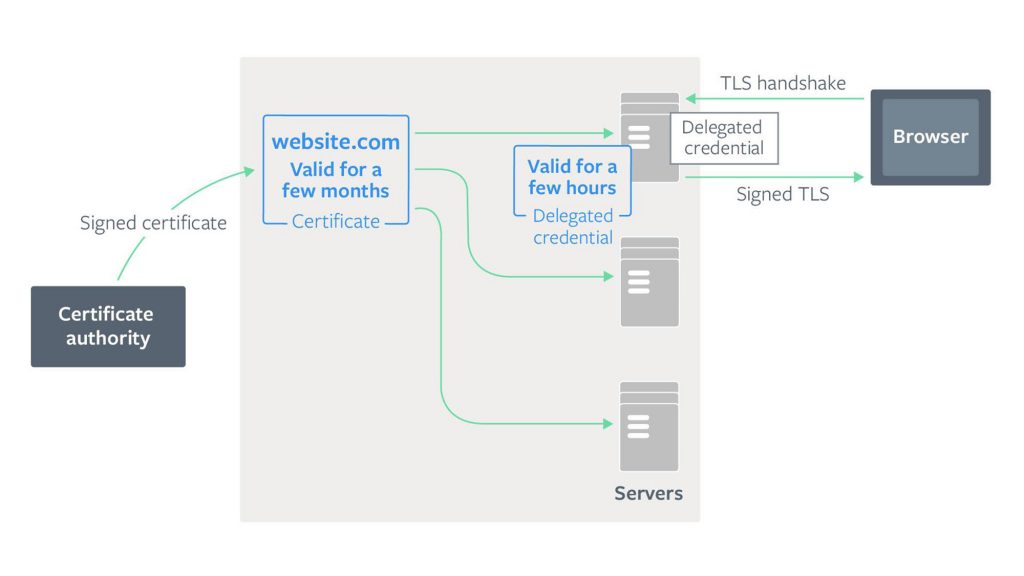
The private key with a shorter period – Delegated credential used generated by the server and not by the Certificate Authority.
The delegated credential consist of the following things:
The delegated credentials secure the connection between a web browser and the server, as it has its own public key.
The website owners can now actively participate in generating a Certificate that has a distinct public and private keys.
Delegated Credential uses a different private key with a shorter period on each server. As it uses a different private key on each server, there is less window of opportunity for a hacker to perform a cyberattack.
Facebook has started supporting Delegated Credentials in its Fizz library.
Try Delegated Credentials yourself by implementing the following steps:
After finishing the above-mentioned steps, it will look as per the below image:
To test if your browser supports delegated credentials for TLS, you can visit the following sites:
fbdelegatedcredentials.com← By Facebook
kc2kdm.com/delegated.html← By Mozilla
When a user connects to a website with a browser supporting delegated credentials, then the server provides a short-lived token to a browser for authentication, instead of using an actual CA Certificate. As the leaf certificate signs the delegated credentials, the chain of trust maintained.
The development of such technology has overcome the limitations of keyless SSL that benefit the customers. It’s great to see big tech giants are coming up with new ideas to secure the internet.
Image source: https://engineering.fb.com/wp-content/uploads/2019/10/DelegatedC.jpg